Practice the breach before it happens
Interactive tabletop exercises your team can run on demand. Scored, benchmarked, and audit-ready.
No signup required. Try a demo scenario in 5 minutes.
Initial Detection
Your phone woke you 6 minutes ago. You're now staring at Splunk from your laptop at the kitchen table. Three radiology file servers are under active encryption. Every minute you wait, it finds more targets.
Key Questions
Discuss with your team:
- 1 What is the blast radius if you wait 15 more minutes to gather data?
- 2 Could isolating systems disrupt any active patient care at 3 AM?
- 3 Is the vendor portal compromise confirmed enough to justify the disruption?
How should the team respond to this active encryption event?
Priya triggers CrowdStrike network containment at 02:54 AM. The encryption stops within 90 seconds. Final count: 18,247 encrypted files — all backed up within the last 4 hours.
Sources: IBM Cost of a Data Breach 2025, Ponemon Institute
HOW IT WORKS
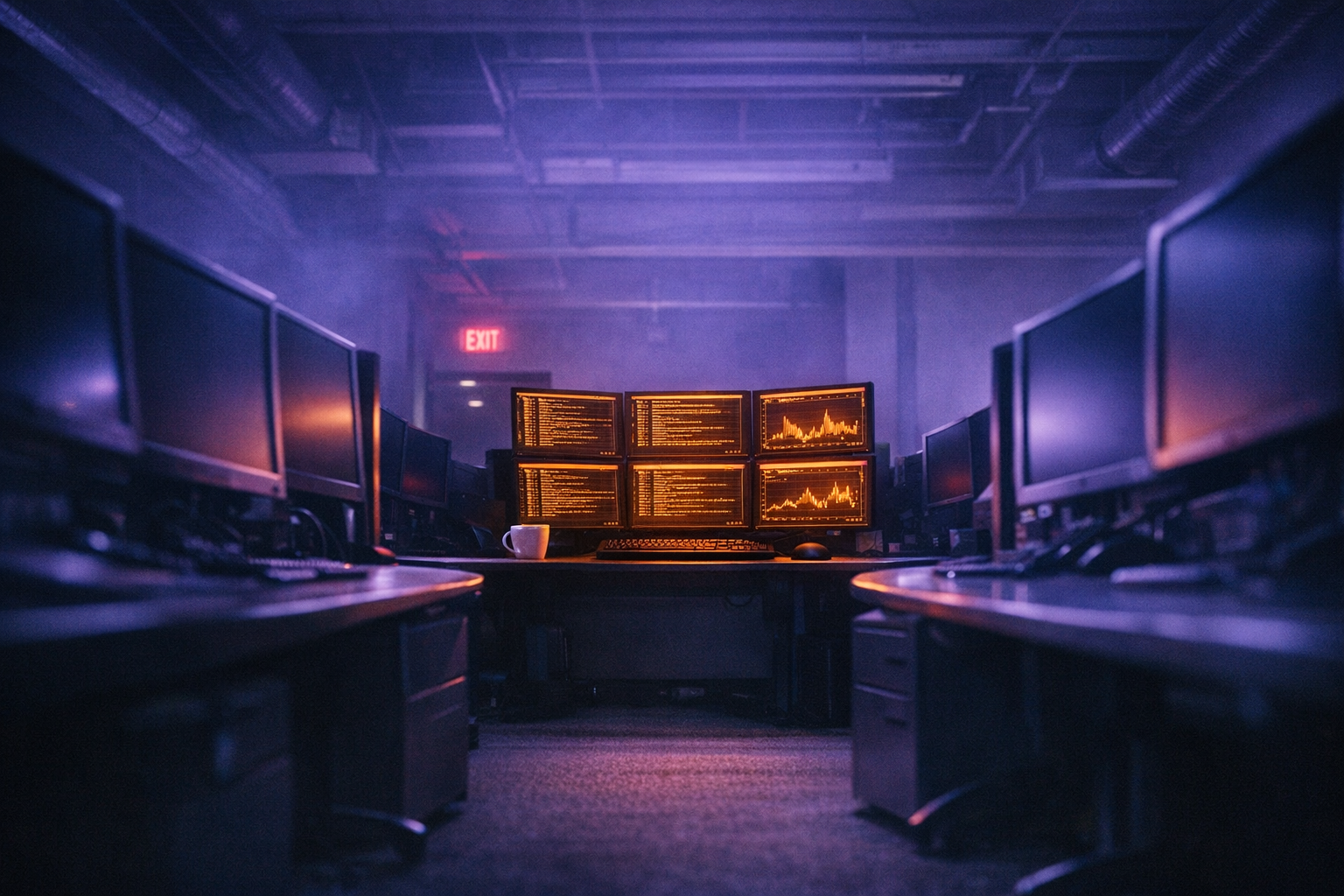
GATHER
Your team joins a call or room. Share your screen with the command center.
BRIEF
The scenario unfolds. Evidence accumulates. Alerts fire. Emails arrive.
DECIDE
Discuss as a team. Debate the options. Make the call.
DEBRIEF
See your score and competency breakdown. Compare your performance to peer teams. Identify training gaps for your next session.
SEE IT IN ACTION
THE SCENARIO UNFOLDS
Every scenario is grounded in real-world threat intelligence. The tactics, techniques, and procedures mirror what adversaries actually use—so your team trains against the threats they'll face.
PHASE 1: INITIAL DETECTION
09:47 AMYour Monday morning coffee is interrupted by a cascade of alerts. The security operations center has flagged unusual outbound traffic from a workstation in the finance department. At the same time, an employee has forwarded a suspicious email to the security team.
The clock is ticking. Every minute counts.
EVIDENCE ARRIVES
Realistic alerts from your SIEM. Phishing emails in your inbox. Slack messages from concerned employees. Evidence arrives through the same channels you use every day.
Unusual outbound traffic detected
YOUR TEAM DEBATES
This is where tabletop exercises shine. Guided prompts help your team discuss how to leverage your incident response plan, which workflows to trigger, and who needs to be in the room.
Discussion Points
Consider these questions with your team:
- 1What does our IR plan say about suspected data exfiltration?
- 2At what point do we trigger the legal/privacy escalation workflow?
- 3Who from leadership needs to be in the room for containment decisions?
MAKE THE CALL
In a real incident, every decision has consequences. Here, your choices drive the scenario forward—isolate too late and the attacker pivots. Escalate too early and you've disrupted the business.
How should we respond to the suspected data exfiltration?
SEE THE CONSEQUENCES
Every decision has tradeoffs. See the immediate consequences of your choice and understand how it affects the rest of the exercise.
KNOW WHERE YOU STAND
Track your team's performance over time. See how you stack up against peers in your industry. Know exactly where to focus your next training investment.
Competency Assessment
You scored better than 72% of teams.
PRACTICE REAL THREATS. NOT POWERPOINT.
A growing library of hyper-realistic scenarios mapped to MITRE ATT&CK® techniques. New scenarios added monthly.

OPERATION MIDNIGHT CIPHER
A ransomware attack strikes a healthcare provider at 2:47 AM. You're the incident commander.

SILENT EXTRACTION
APT41 has exfiltrated six months of clinical trial data from a pharma company. Discovered when a competitor publishes eerily similar results.
OPERATION CHARTPHANTOM
A compromised open-source charting library has turned 340 financial institutions into beachheads. Notify the industry during a $6.8B merger — or stay silent?

GRID SHADOW
Compromised firmware on smart grid relays deployed during a record heat wave. Roll back and risk grid safety, or keep running compromised systems?

CLONED PORTAL
A cloned government citizen services portal is harvesting SSNs. Discovered by a journalist, not your SOC. Disclose and risk trust — or stay quiet?

DEAD MAN'S SWITCH
A departing admin planted time-delayed destructive scripts. 48 hours until they fire — two days before finals for 30,000 students.
WHY BREACHDECK
TRADITIONAL APPROACH
BREACHDECK
Better exercises. A fraction of the cost. On your schedule.
A traditional tabletop exercise: $25,000+
Or train your team all year:
STARTER
One scenario per year with unlimited runs — ideal for annual compliance exercises
- 1 scenario per year, unlimited runs
- Choose from 5 core scenarios
- SSO authentication
- Full debrief & scoring
- PDF report export
- Email support
TEAM
Full access for teams that train continuously
- Everything in Starter
- Unlimited scenarios & runs
- Full scenario library
- Team benchmarking
- Advanced analytics & reporting
- Priority support
ENTERPRISE
Tailored to your environment and threat landscape
- Everything in Team
- SCIM provisioning
- Custom-built scenarios
- Dedicated account manager
- SLA & uptime guarantee
FREQUENTLY ASKED QUESTIONS
PRODUCT
How long does an exercise take?
Most exercises run 30–60 minutes depending on scenario complexity and team discussion depth. Beginner scenarios start at 30 minutes; advanced scenarios with multiple decision branches take closer to 60.
How many people can participate?
Exercises work best with 4–12 participants. One person shares their screen with the command center while the full team discusses and debates decisions together.
Do I need a facilitator?
No. Breachdeck guides the exercise automatically—presenting evidence, prompting decisions, and managing the scenario timeline. Your team focuses on response, not logistics.
What do I get at the end of an exercise?
A scored debrief with competency breakdowns across containment, communication, compliance, and business impact. You also get a one-click PDF export for audit documentation and team review.
COMPLIANCE & AUDIT
Which frameworks require tabletop exercises?
PCI DSS 4.0 (Req 12.10.2), SOC 2 (CC7.1/CC7.2), ISO 27001 (A.16.1.5), and GDPR (Article 32) all require periodic testing of incident response plans. HIPAA and CMMC have similar requirements.
What documentation does Breachdeck produce?
Each exercise generates a timestamped PDF report with scenario details, team decisions, outcome analysis, and competency scores. Reports are designed to satisfy auditor expectations for IR plan testing evidence.
Can I use exercise reports for SOC 2 / HIPAA / PCI DSS audits?
Yes. Reports include the exercise date, participants, scenario scope, decisions made, and scored outcomes—the key evidence auditors look for when reviewing IR testing controls.
SCENARIOS & REALISM
How realistic are the scenarios?
Every scenario is mapped to the MITRE ATT&CK framework and modeled on real-world attack patterns. Evidence artifacts include SIEM alerts, email threads, system logs, and executive communications.
Are scenarios based on real incidents?
Scenarios are inspired by real-world attack patterns and publicly documented incidents, adapted into interactive exercises with branching decision trees and multiple outcome paths.
How often are new scenarios added?
New scenarios are added monthly to cover emerging threats and evolving attack techniques. The scenario library spans ransomware, data breaches, insider threats, supply chain attacks, BEC, and more.
Can I request custom scenarios?
Enterprise plans include custom scenario development tailored to your industry, threat landscape, and compliance requirements. Contact us to discuss your needs.